Cybersecurity is no longer a secondary consideration in digital transformation. It is a foundational requirement. As enterprises accelerate cloud adoption, API integration, automation, and data exchange, the traditional “bolt-on” security model has become obsolete.
In the past, organizations would design systems, deploy applications, and then involve security teams for final testing. That approach worked when IT environments were static and perimeter-based. Today’s digital ecosystems are dynamic, distributed, and continuously evolving. Security must evolve accordingly.
Modern cybersecurity is designed into architecture from the very beginning.
The Shift From Reactive to Proactive Cybersecurity
Historically, It is focused on perimeter defense firewalls, antivirus software, and network gateways. The idea was to protect the boundary and assume internal systems were safe.
However, with cloud infrastructure, remote work, SaaS applications, and API-driven platforms, the perimeter has disappeared. Attack surfaces are constantly changing. Cyber threats are more sophisticated, automated, and financially motivated.
This shift has forced organizations to move from reactive security responses to proactive, built-in cybersecurity strategies. Instead of responding to incidents, companies now focus on preventing vulnerabilities during development and deployment.
Why Bolt-On Cybersecurity Fails in Modern IT Environments
Bolt-on cybersecurity introduces risk because:
- Security gaps are discovered too late in development
- Infrastructure misconfigurations go unnoticed until exposed
- Vulnerabilities are patched instead of prevented
- Compliance requirements become last-minute obstacles
- Security teams operate separately from engineering teams
This reactive model increases operational friction and creates unnecessary exposure.
In contrast, built-in cybersecurity embeds security controls directly into architecture, workflows, and governance processes.
Security by Design: The New Enterprise Standard
Security by design means its principles are integrated throughout the software development lifecycle and infrastructure planning stages.
This includes:
- Secure coding practices from the first line of code
- Automated vulnerability scanning in CI/CD pipelines
- Dependency monitoring for third-party libraries
- Identity-based access controls
- Encryption at rest and in transit
- Continuous compliance validation
Cybersecurity becomes an ongoing process rather than a one-time review.
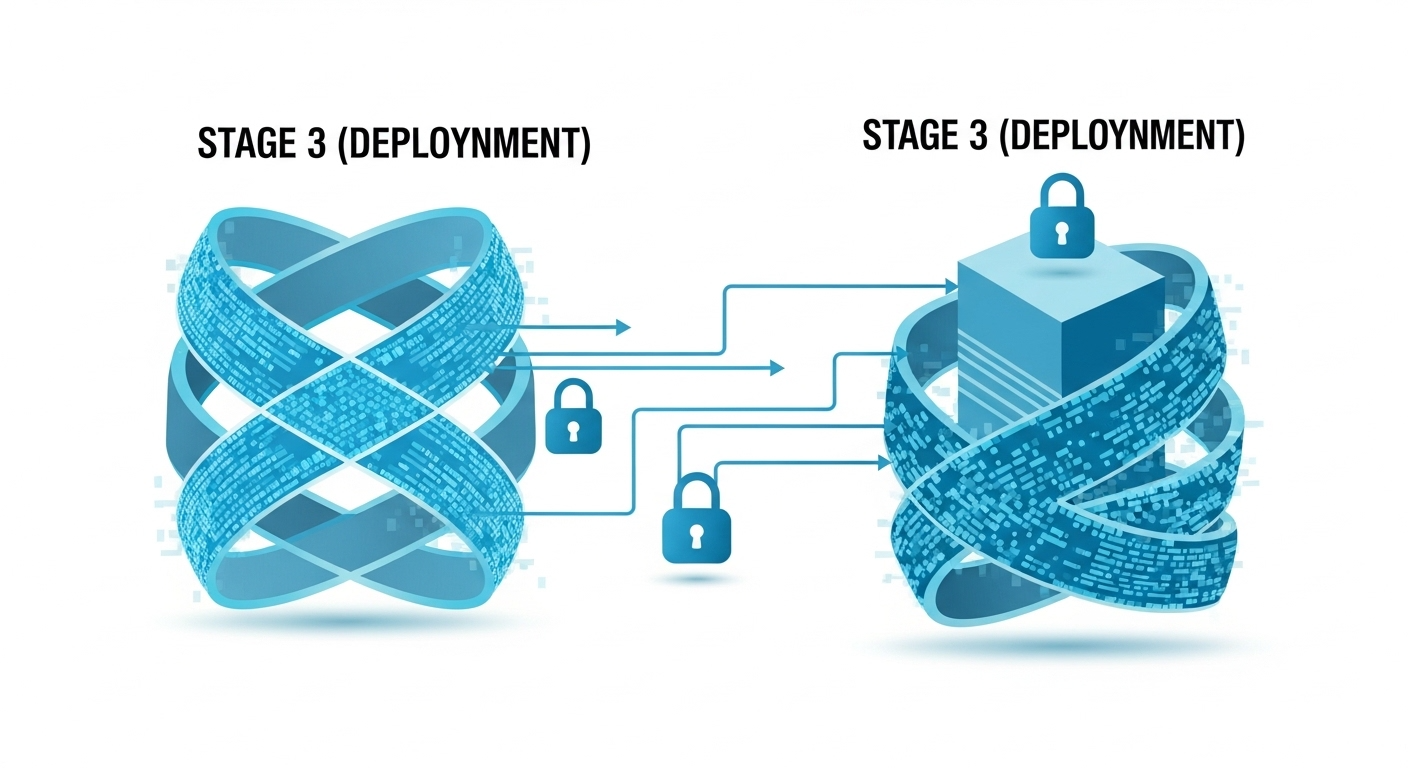
DevSecOps: Integrating Cybersecurity Into Delivery
One of the most significant evolutions in cybersecurity is the rise of DevSecOps the integration of development, security, and operations.
Under DevSecOps:
- Security testing runs automatically with every code commit
- Infrastructure-as-code configurations are validated before deployment
- Secrets management is automated
- Policy enforcement is embedded into pipelines
It is shifts left in the development lifecycle, identifying risks before systems reach production.
This approach reduces breach probability and improves release confidence.
Zero Trust Architecture and Continuous Verification
Another major cybersecurity advancement is the adoption of zero trust architecture.
Zero trust operates on a simple principle: never trust, always verify.
Every user, device, API call, and system interaction must be authenticated and authorized continuously. This includes:
- Multi-factor authentication
- Least-privilege access policies
- Micro-segmentation of networks
- Continuous monitoring of behavioral anomalies
It becomes identity-driven rather than perimeter-based.
Cybersecurity in Cloud-Native Environments
Cloud adoption has redefined cybersecurity responsibilities. Shared responsibility models require organizations to secure:
- Application layers
- Access permissions
- Data storage configurations
- API gateways
- Container environments
That is integrates tools such as:
- Cloud security posture management (CSPM)
- Real-time threat detection
- Automated compliance audits
- Infrastructure configuration monitoring
This proactive approach prevents misconfigurations that often lead to breaches.
The Business Case for Built-In Cybersecurity
It is not only a technical necessity it is a business imperative.
Data breaches result in:
- Financial penalties
- Regulatory fines
- Legal exposure
- Reputational damage
- Customer attrition
The cost of remediation significantly exceeds the cost of prevention.
Organizations that build cybersecurity into their systems experience:
- Reduced downtime
- Improved regulatory compliance
- Stronger stakeholder trust
- Faster incident response
- Greater operational resilience
It’s directly impacts long-term business stability.
Governance, Compliance, and Executive Responsibility
Modern cybersecurity requires executive oversight. Boards and C-level leadership must now:
- Define acceptable risk levels
- Allocate budgets
- Align security metrics with business KPIs
- Review incident response readiness
- Promote company-wide security awareness
That strategy is now inseparable from digital strategy.
Without executive alignment, built-in cybersecurity initiatives lose effectiveness.
The Future of Cybersecurity Architecture
This will continue evolving toward automation and intelligence.
Emerging developments include:
- AI-driven threat detection
- Automated response playbooks
- Behavioral anomaly monitoring
- Compliance-as-code frameworks
- Integrated security analytics dashboards
Security will increasingly operate as a self-adjusting layer within enterprise systems.
The goal is not visible security it is resilient architecture.
Conclusion
Cybersecurity is no longer an optional enhancement or final-stage audit. In a world of continuous deployment, cloud-native systems, distributed APIs, and evolving threat landscapes, security must be embedded into the DNA of digital systems.
Organizations that treat it as infrastructure not an accessory build stronger, more resilient digital ecosystems. Those that rely on bolt-on defenses increase exposure with every integration and every deployment.
In today’s digital economy, It is not a feature. It is the foundation of sustainable transformation.
For more Details let’s connect on Contact Us