For more than a decade, application security programs were built primarily around static analysis. Security teams scanned code before deployment, generated vulnerability reports, and sent findings back to developers for remediation. This “scan → fix → release” cycle became standard practice across enterprises.
But in 2026, that model alone is no longer sufficient.
Modern applications are dynamic, distributed, API-driven, and continuously deployed. Static testing still plays an important role but it cannot keep up with real-time threats, cloud-native complexity, and evolving attack techniques.
As a result, runtime security is overtaking static-only approaches as the dominant strategy in modern application security.
Security is shifting from prediction to protection.
The Traditional Static Security Model
Static Application Security Testing (SAST) analyzes source code without executing it. It identifies patterns that may represent vulnerabilities, such as:
- SQL injection risks
- Cross-site scripting flaws
- Hard-coded credentials
- Unsafe memory handling
- Known vulnerable dependencies
The strength of static testing lies in early detection. By scanning code before release, teams can reduce risk before deployment.
However, static analysis has inherent limitations.
The Structural Limitations of Static-Only Security
1. Lack of Runtime Context
Static tools analyze code in isolation. They cannot see:
- How services interact at runtime
- Whether vulnerable code paths are actually reachable
- Which APIs are publicly exposed
- How user roles affect access control
Without runtime context, risk assessment becomes theoretical.
2. High False Positive Rates
Security teams often spend significant time triaging findings that may not be exploitable in practice. This creates:
- Alert fatigue
- Remediation delays
- Developer frustration
- Reduced trust in security tools
When everything looks critical, nothing feels urgent.
3. Inability to Detect Business Logic Abuse
Many modern attacks do not exploit coding flaws they exploit flawed workflows.
For example:
- Manipulating pricing logic
- Bypassing rate limits
- Abusing API sequencing
- Circumventing authentication flows
Static analysis cannot simulate or detect these runtime abuses.
4. Cloud-Native and Microservices Complexity
Modern systems include:
- Containers
- Serverless functions
- Dynamic infrastructure
- Third-party APIs
- Continuous deployments
Static scans performed before deployment cannot account for configuration drift, environment variables, or evolving infrastructure states.
Why Runtime Security Is Gaining Dominance
Runtime security shifts the focus from code inspection to live behavioral monitoring.
Instead of asking:
“Could this code be vulnerable?”
Runtime security asks:
“Is this vulnerability being exploited right now?”
This shift offers several advantages.
Real-Time Threat Detection
Runtime systems monitor live traffic and execution patterns. They can detect:
- Injection attempts
- API abuse
- Token manipulation
- Privilege escalation
- Suspicious request patterns
- Exploit payload signatures
This allows organizations to block threats instantly rather than discovering them after damage occurs.
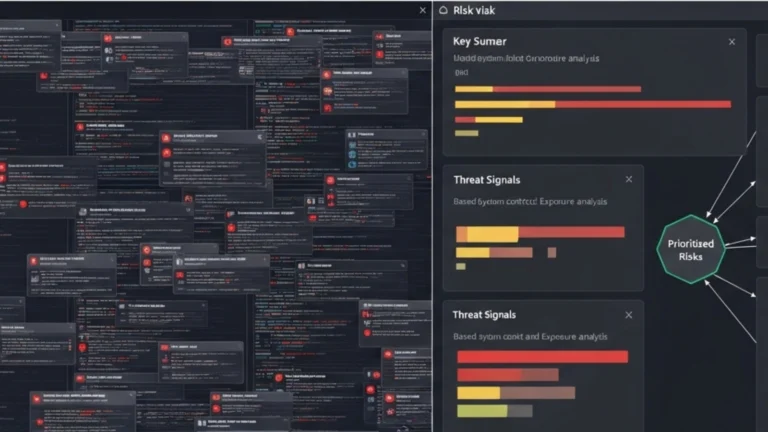
Context-Aware Risk Evaluation
Runtime protection evaluates:
- User identity and permissions
- Network exposure
- Deployment environment
- Data sensitivity
- Active exploit behavior
This contextual intelligence allows security teams to prioritize genuine threats over theoretical risks.
Runtime Application Self-Protection (RASP)
RASP solutions embed directly into the application runtime environment. They:
- Monitor execution
- Detect malicious behavior
- Block exploit attempts in real time
Unlike perimeter defenses, RASP protects applications internally even if attackers bypass external controls.
Interactive Application Security Testing (IAST)
IAST operates during testing phases but leverages runtime instrumentation. It provides deeper insight into:
- Code coverage during tests
- Real execution paths
- Confirmed vulnerabilities
IAST bridges the gap between static and dynamic testing.
Runtime Protection and DevSecOps
As organizations adopt DevSecOps and continuous deployment, security must operate at the same speed as development.
Runtime protection supports:
- Rapid release cycles
- Frequent feature updates
- Continuous validation
- Immediate feedback loops
Security becomes an always-on layer rather than a pre-release checkpoint.
Business Impact of Runtime Security
The shift toward runtime security is not purely technical it is strategic.
Revenue Protection
Production attacks directly affect transactions, subscription renewals, and user trust. Runtime blocking mechanisms reduce financial loss.
Reduced Incident Response Time
By detecting and blocking attacks instantly, runtime security lowers:
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
Faster containment reduces operational disruption.
Compliance and Regulatory Alignment
Modern compliance frameworks increasingly require:
- Continuous monitoring
- Active incident detection
- Real-time reporting capabilities
Runtime security supports these mandates.
Runtime vs Static: A Layered Strategy
It is important to emphasize that runtime security does not eliminate the need for static analysis.
A mature strategy includes:
- SAST for early code review
- DAST for simulated attack testing
- IAST for execution-aware scanning
- RASP for production protection
- Dependency scanning for supply chain security
The key difference in 2026 is prioritization. Static-only strategies are no longer enough.
Runtime validation is becoming central.
Emerging Trends in Runtime Security
AI-Driven Behavioral Detection
Machine learning models now analyze traffic anomalies and detect patterns that traditional rule-based systems miss.
Zero-Trust Runtime Policies
Applications enforce strict access controls internally, verifying every request based on identity and context.
Runtime Security Observability
Security metrics are increasingly integrated into observability dashboards alongside performance and reliability metrics.
This unifies security, operations, and engineering teams.
Challenges to Adoption
Runtime protection introduces considerations:
- Performance overhead concerns
- Integration complexity
- Need for skilled interpretation of alerts
- Balancing automation with human oversight
However, as tooling matures, these barriers are decreasing.
The Future of Application Security
The future of application security is:
- Continuous
- Context-aware
- Runtime-driven
- Business-aligned
Security will increasingly operate inside the application itself, monitoring execution behavior rather than relying solely on pre-deployment predictions.
Applications will defend themselves dynamically.
Conclusion
Static analysis established the foundation of secure development practices. But in today’s fast-moving, cloud-native environments, it cannot stand alone.
Runtime security provides real-time visibility, contextual intelligence, and active protection against modern threats.
The organizations that succeed in 2026 and beyond will adopt layered strategies but they will prioritize runtime defense as a core capability.
Static testing identifies potential weaknesses.
Runtime security stops real attacks.
The shift is not optional. It is evolutionary.
For more Contact US