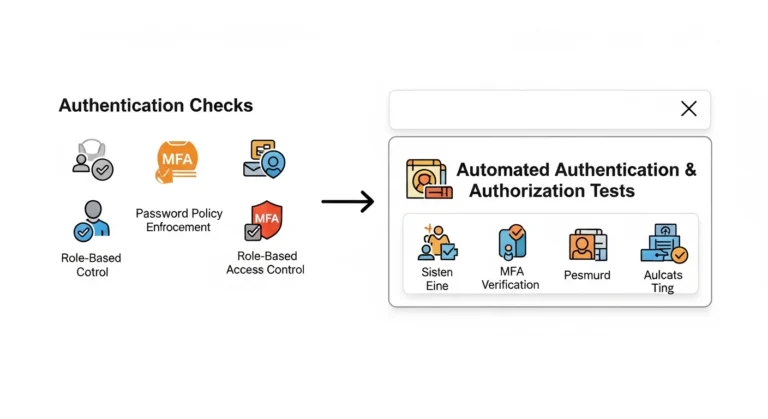
Tag: Secure Software Development
Advanced Threat Modeling Strategies for Stronger Security Testing in 2026
For years, threat modeling was treated as a separate security exercise typically conducted at the beginning of a…
Read More →Cybersecurity Strategies That Protect Your Business from Serious Threats
Cybersecurity is no longer a secondary consideration in digital transformation. It is a foundational requirement. As enterprises accelerate…
Read More →